There is a specific way to change the SSRS service account if you strait forward change the service account then after restart of SSRS when you try to access reports you will receive below error.
The report server cannot decrypt the symmetric key used to access sensitive or encrypted data in a report server database. You must either restore a backup key or delete all encrypted content and then restart the service. Check the documentation for more information. (rsReportServerDisabled) Get Online
In the SSRS log you can see the below log
Cause:
The Report Server service uses the symmetric key to access the encrypted data in a report server database. This symmetric key is encrypted by using an asymmetric public key that corresponds to the computer and the user account that is used to run the Report Server service. When you change the user account that is used to run the Report Server service, the report server cannot use the asymmetric public key to decrypt the symmetric key. Therefore, the Report Server service cannot use the symmetric key to access the data from the report server database.
Please follow below mentioned steps to backup\restore encryption keys
- Start the Report Server Windows service and Report Server Web service
- Backup your encryption keys via
RSKeyMgmt -e -f filename -p strongPassword
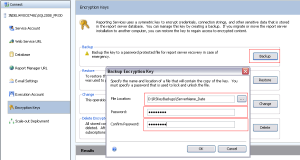
You can also take backup from SSRS configuration manager as shown below.
Open SSRS configuration manager and go to Encryption keys in TAB and then on right pane click backup button, enter location and a strong password.
- Remove the reference to the encryption key (locate the InstallationID in the “%ProgramFiles%\Microsoft SQL Server\MSSQL\ReportingServices\ReportServer\RSReportServer.config“ file

RSKeyMgmt -r InstallationIDGuid
- Stop IIS
- Stop the Report Server Windows service
- Change the user account on the Report Server Windows service
- Start IIS
- Start the Report Server Windows service
- Apply the encryption key previously backed up
RSKeyMgmt -a -f filename -p strongPassword

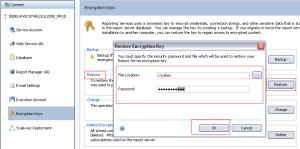
The same can be done from GUI as shown below.
Now you have successfully done backup\restore of encryption keys.




Reblogged this on a record of a developer and commented:
This saved me a bit of time. Now all i need to do is schedule a down time…